Hamo AI Achieves Full Technical PHIPA Compliance
Hamo AI Achieves Full Technical PHIPA Compliance, Setting a New Standard for Privacy in AI Mental Health Care
Toronto, Canada — April 14, 2026 — Hamo AI Technology Ltd. today announced the successful completion of a comprehensive technical compliance audit under PHIPA 6.1 (Personal Health Information Protection Act). The audit covers all four components of the Hamo AI platform: the hamo-ume backend API, Hamo Pro therapist dashboard, Hamo Client user application, and Hamo Portal management console.
This milestone reflects Hamo AI's commitment to operating at the highest standards of data security and user privacy — not as an afterthought, but as a foundational design principle from day one.
Why PHIPA Compliance Matters
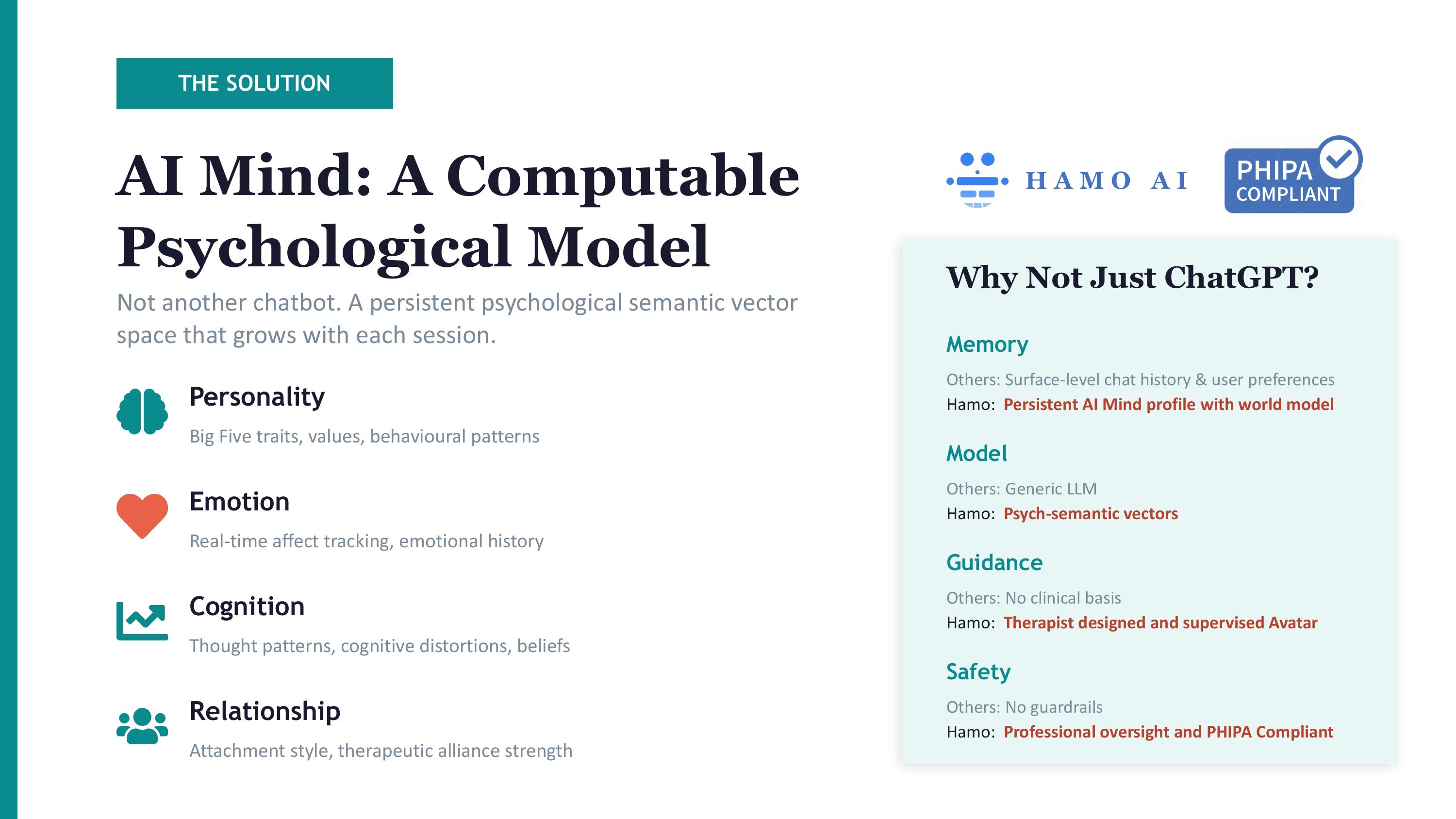
In a landscape where AI mental health tools are proliferating rapidly, most general-purpose AI systems — including ChatGPT, Gemini, and other consumer LLMs — operate with no clinical guardrails, no data residency controls, and no healthcare-grade privacy protections. Users who share sensitive mental health information with these tools have no assurance about where their data is stored, who can access it, or how it is protected.
PHIPA is Ontario's gold standard for protecting personal health information. For any AI system handling sensitive therapeutic conversations, achieving PHIPA compliance is not optional — it is a fundamental obligation to users.
Hamo AI is building to meet that obligation.
Seven Layers of PHIPA-Compliant Security
The following technical controls have been fully implemented across the Hamo AI platform:
1. Encryption in Transit (PHIPA 6.1.1)
All data transmitted between users and the Hamo AI platform is protected by TLS 1.2+ encryption. The backend API is served exclusively over HTTPS via AWS Elastic Beanstalk with ACM-managed certificates (*.hamo.ai). All three frontends (Hamo Pro, Hamo Client, Hamo Portal) enforce HTTPS through CloudFront, with automatic HTTP-to-HTTPS redirection. All CORS allowlists permit only HTTPS origins.
2. Encryption at Rest — Customer-Managed Keys (PHIPA 6.1.2)
All stored personal health information is encrypted using AES-256 with Customer-Managed KMS Keys (CMK). All 11 DynamoDB tables — including users, avatars, ai_minds, psvs_profiles, conversation_sessions, conversation_messages, and refresh_tokens — are encrypted with SSE-KMS using dedicated CMKs (alias/hamo-phi-*). IAM policies restrict KMS access to authorized DynamoDB service operations only. S3 storage for avatar and media assets uses AES-256 SSE-S3 encryption with TLS-enforced transmission.
3. Role-Based Access Control (PHIPA 6.1.3)
The platform enforces strict three-tier role separation: PORTAL_ADMIN (management), THERAPIST (clinical), and CLIENT (end-user). Every API endpoint is protected by rbac_middleware that validates JWT role claims against a route-prefix whitelist (/api/portal/*, /api/pro/*, /api/client/*). A formal API permission matrix is maintained and reviewed quarterly.
4. Multi-Factor Authentication (PHIPA 6.1.4)
MFA is mandatory on all login entry points across all three user-facing applications. The system implements a 6-digit email verification code with a 5-minute expiry and a maximum of 3 attempts. Trusted-device recognition allows verified users to skip MFA for 30 days via HttpOnly cookies. MFA emails are delivered through AWS SES with full bilingual (Chinese/English) support.
5. Comprehensive Audit Logging (PHIPA 6.1.5)
Every access to or modification of personal health information is automatically captured in the hamo_audit_logs DynamoDB table. The HTTP middleware records action, resource_type, resource_id, user_id, user_email, user_role, ip_address, and timestamp for every PHI API request. GSI indexes enable efficient audit trails by user and resource. Authentication events — including LOGIN, LOGIN_FAILED, and PASSWORD_RESET — are logged separately. The Portal admin console provides a secure audit query interface.
6. Password Security — bcrypt Hashing (PHIPA 6.1.7)
All user passwords are stored using bcrypt with cost factor 12, replacing the legacy SHA-256 implementation. A transparent migration ensures that existing users are automatically upgraded to bcrypt on their next successful login. Password complexity requirements enforce a minimum of 8 characters with uppercase, lowercase, numeric, and special character requirements.
7. Session Management with Idle Timeout (PHIPA 6.1.8)
Sessions are protected by HttpOnly + Secure cookies with a 30-minute idle timeout. JWT access tokens expire after 24 hours; refresh tokens after 7 days. The /api/auth/refresh endpoint validates last_activity on every request and rejects sessions that have been idle beyond the threshold. The backend supports dual-mode authentication (Bearer header and HttpOnly cookie) to enable a seamless transition across all frontends.
How This Compares to Generic AI Tools
| ChatGPT / Gemini | Hamo AI | |
|---|---|---|
| Data Encryption at Rest | Standard cloud defaults | AES-256 CMK (customer-controlled) |
| Access Control | Account-level only | RBAC with 3 clinical roles |
| Multi-Factor Auth | Optional | Mandatory on all entry points |
| Audit Trail | None | Full PHI access logging |
| Session Idle Timeout | None | 30-minute enforced timeout |
| Password Security | Platform-managed | bcrypt (cost=12) |
| Privacy Regulation | No healthcare compliance | PHIPA 6.1 compliant |
“When someone shares their most vulnerable moments with an AI system, they deserve to know that their privacy is protected by the highest technical standards available. PHIPA compliance is our commitment — not just to regulators, but to every user, every therapist, and every family that trusts us with their mental health journey. This is what it means to build AI responsibly.”
— Chris Cheng, Founder and CEO of Hamo AI
What's Next
Hamo AI's continued compliance roadmap includes enabling annual KMS key rotation, implementing account lockout policies, and establishing CloudWatch monitoring for anomalous access patterns.
Hamo AI is actively working with mental health professionals and institutions to build partnerships grounded in clinical integrity, professional oversight, and user-first privacy protection.
About Hamo AI
Hamo AI Technology Ltd. is a Canada-based artificial intelligence company building next-generation AI-Powered Therapist Avatar System. We are developing a comprehensive AI therapy platform called “Hamo” that connects mental health professionals with clients through AI-powered therapy avatars. The ecosystem consists of three interconnected applications: Hamo Pro (therapist dashboard for creating and managing AI avatars), Hamo Client (client interface for interacting with therapy avatars), and Hamo-UME (Unified Mind Engine, backend API). The platform aims to make mental health support more accessible while maintaining professional oversight through professional therapists who create and manage the AI avatars.
Media Contact
Hamo AI Technology Ltd.
Email: socialmedia@hamo.ai
Website: www.hamo.ai
Address: 108 College St, Schwartz Reisman Campus, SUITE W640, Toronto ON M5G 0C6, Canada